PEAS
I got the initial foothold and transferred the linpeash.sh to the target system over HTTP
www-data@openadmin:/tmp$ ./linpeas.shExecuting linpeas.sh
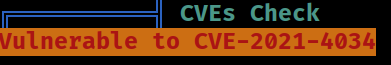 peas discovered that the target system is vulnerable to cve-2021-4034
peas discovered that the target system is vulnerable to cve-2021-4034
╔══════════╣ Executing Linux Exploit Suggester
╚ https://github.com/mzet-/linux-exploit-suggester
cat: write error: Broken pipe
cat: write error: Broken pipe
cat: write error: Broken pipe
cat: write error: Broken pipe
cat: write error: Broken pipe
[+] [CVE-2021-4034] PwnKit
details: https://www.qualys.com/2022/01/25/cve-2021-4034/pwnkit.txt
exposure: probable
tags: [ ubuntu=10|11|12|13|14|15|16|17|18|19|20|21 ],debian=7|8|9|10|11,fedora,manjaro
download url: https://codeload.github.com/berdav/CVE-2021-4034/zip/main
[+] [CVE-2021-3156] sudo Baron Samedit
details: https://www.qualys.com/2021/01/26/cve-2021-3156/baron-samedit-heap-based-overflow-sudo.txt
exposure: probable
tags: mint=19,[ ubuntu=18|20 ], debian=10
download url: https://codeload.github.com/blasty/CVE-2021-3156/zip/main
[+] [CVE-2021-3156] sudo Baron Samedit 2
details: https://www.qualys.com/2021/01/26/cve-2021-3156/baron-samedit-heap-based-overflow-sudo.txt
exposure: probable
tags: centos=6|7|8,[ ubuntu=14|16|17|18|19|20 ], debian=9|10
download url: https://codeload.github.com/worawit/CVE-2021-3156/zip/main
[+] [CVE-2018-18955] subuid_shell
details: https://bugs.chromium.org/p/project-zero/issues/detail?id=1712
exposure: probable
tags: [ ubuntu=18.04 ]{kernel:4.15.0-20-generic},fedora=28{kernel:4.16.3-301.fc28}
download url: https://github.com/offensive-security/exploitdb-bin-sploits/raw/master/bin-sploits/45886.zip
comments: CONFIG_USER_NS needs to be enabled
[+] [CVE-2022-32250] nft_object UAF (NFT_MSG_NEWSET)
details: https://research.nccgroup.com/2022/09/01/settlers-of-netlink-exploiting-a-limited-uaf-in-nf_tables-cve-2022-32250/
https://blog.theori.io/research/CVE-2022-32250-linux-kernel-lpe-2022/
exposure: less probable
tags: ubuntu=(22.04){kernel:5.15.0-27-generic}
download url: https://raw.githubusercontent.com/theori-io/CVE-2022-32250-exploit/main/exp.c
comments: kernel.unprivileged_userns_clone=1 required (to obtain CAP_NET_ADMIN)
[+] [CVE-2022-2586] nft_object UAF
details: https://www.openwall.com/lists/oss-security/2022/08/29/5
exposure: less probable
tags: ubuntu=(20.04){kernel:5.12.13}
download url: https://www.openwall.com/lists/oss-security/2022/08/29/5/1
comments: kernel.unprivileged_userns_clone=1 required (to obtain CAP_NET_ADMIN)
[+] [CVE-2021-22555] Netfilter heap out-of-bounds write
details: https://google.github.io/security-research/pocs/linux/cve-2021-22555/writeup.html
exposure: less probable
tags: ubuntu=20.04{kernel:5.8.0-*}
download url: https://raw.githubusercontent.com/google/security-research/master/pocs/linux/cve-2021-22555/exploit.c
ext-url: https://raw.githubusercontent.com/bcoles/kernel-exploits/master/CVE-2021-22555/exploit.c
comments: ip_tables kernel module must be loaded
[+] [CVE-2019-15666] XFRM_UAF
details: https://duasynt.com/blog/ubuntu-centos-redhat-privesc
exposure: less probable
download url:
comments: CONFIG_USER_NS needs to be enabled; CONFIG_XFRM needs to be enabled
[+] [CVE-2017-5618] setuid screen v4.5.0 LPE
details: https://seclists.org/oss-sec/2017/q1/184
exposure: less probable
download url: https://www.exploit-db.com/download/https://www.exploit-db.com/exploits/41154
[+] [CVE-2017-0358] ntfs-3g-modprobe
details: https://bugs.chromium.org/p/project-zero/issues/detail?id=1072
exposure: less probable
tags: ubuntu=16.04{ntfs-3g:2015.3.14AR.1-1build1},debian=7.0{ntfs-3g:2012.1.15AR.5-2.1+deb7u2},debian=8.0{ntfs-3g:2014.2.15AR.2-1+deb8u2}
download url: https://github.com/offensive-security/exploit-database-bin-sploits/raw/master/bin-sploits/41356.zip
comments: Distros use own versioning scheme. Manual verification needed. Linux headers must be installed. System must have at least two CPU cores.
It also found a list of other vulnerabilities but these aren’t 100% confirmed They require further investigation