RustScan
┌──(kali㉿kali)-[~/archive/htb/labs/pit]
└─$ rustscan -a $IP -b 20000
________________________________________
: https://discord.gg/GFrQsGy :
: https://github.com/RustScan/RustScan :
--------------------------------------
Real hackers hack time ⌛
[~] The config file is expected to be at "/home/kali/.rustscan.toml"
[~] Automatically increasing ulimit value to 5000.
[!] File limit is lower than default batch size. Consider upping with --ulimit. May cause harm to sensitive servers
open 10.10.10.241:22
open 10.10.10.241:80
open 10.10.10.241:9090Nmap
┌──(kali㉿kali)-[~/archive/htb/labs/pit]
└─$ nmap -sC -sV -p22,80,9090 $IP 127 ⨯
Starting Nmap 7.93 ( https://nmap.org ) at 2023-04-07 09:07 CEST
Nmap scan report for 10.10.10.241
Host is up (0.094s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.0 (protocol 2.0)
| ssh-hostkey:
| 3072 6fc3408f6950695a57d79c4e7b1b9496 (RSA)
| 256 c26ff8aba12083d160abcf632dc865b7 (ECDSA)
|_ 256 6b656ca692e5cc76175a2f9ae750c350 (ED25519)
80/tcp open http nginx 1.14.1
|_http-server-header: nginx/1.14.1
|_http-title: Test Page for the Nginx HTTP Server on Red Hat Enterprise Linux
9090/tcp open ssl/zeus-admin?
| fingerprint-strings:
| GetRequest, HTTPOptions:
| HTTP/1.1 400 Bad request
| Content-Type: text/html; charset=utf8
| Transfer-Encoding: chunked
| X-DNS-Prefetch-Control: off
| Referrer-Policy: no-referrer
| X-Content-Type-Options: nosniff
| Cross-Origin-Resource-Policy: same-origin
| <!DOCTYPE html>
| <html>
| <head>
| <title>
| request
| </title>
| <meta http-equiv="Content-Type" content="text/html; charset=utf-8">
| <meta name="viewport" content="width=device-width, initial-scale=1.0">
| <style>
| body {
| margin: 0;
| font-family: "RedHatDisplay", "Open Sans", Helvetica, Arial, sans-serif;
| font-size: 12px;
| line-height: 1.66666667;
| color: #333333;
| background-color: #f5f5f5;
| border: 0;
| vertical-align: middle;
| font-weight: 300;
|_ margin: 0 0 10p
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=dms-pit.htb/organizationName=4cd9329523184b0ea52ba0d20a1a6f92/countryName=US
| Subject Alternative Name: DNS:dms-pit.htb, DNS:localhost, IP Address:127.0.0.1
| Not valid before: 2020-04-16T23:29:12
|_Not valid after: 2030-06-04T16:09:12
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 192.54 secondsThe target system is RHEL based Linux
SSL certificate shows domain information; dms-pit.htb
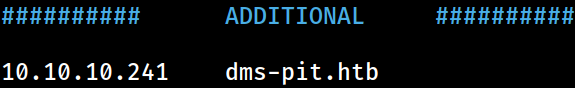 It’s been appended to the
It’s been appended to the /etc/hosts file on Kali for local DNS resolution